Beware of Fake SEO Companies
These days the amount of unsolicited emails that are being received by Businesses advertising Website Design or Search Engine Optimisation is becoming as bad as telemarketers claiming they are with Telstra or Optus trying to con you to switch phone companies.
The easy way to pick the dodgy operators quickly is to look at their email addresses.
If the email was sent from a free email service such as Gmail, Hotmail or Yahoo for example – do not reply to them – do not trust them.
Every reputable Website and SEO company in the world will only send emails from their domain name servers. For example, emails from Redback Web Solutions will always have an email address ending in redbackwebs.com.au such as info@redbackwebs.com.au.
Any internet business that hides behind a free email service smells of distrust immediately. If you reply to an email from one of these addresses, you can almost guarantee that you will end up on a whole stack of mailing lists increasing the amount of spam that you receive.
Personally I hate it. Redback Web Solutions would receive at least 5 or 6 of these emails a day. As a Company that specialises in Web Development and Search Engine Optimisation, sending spam email to Redback Web Solutions trying to sell SEO services or Website design is like trying to sell sand to the Arabs! Plus they clearly these companies or individuals haven’t done any market research – even though they claim in their emails that they have carefully viewed our site.
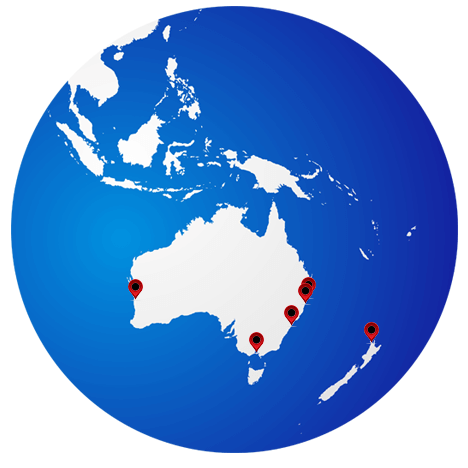
If you are going to re-develop your website, or start a marketing campaign – then only choose a reputable company that is actually based in Australia. Not India, not Singapore, not the US, not the Phillapines!
Here are some additional tips on identifying spam emails and and a link on how to whitelist important businesses so that their emails dont end up in your junk folder if you improve your email security.
How to whitelist Redback Web Solutions.
Protecting Against Spam Emails
Spammers collect email addresses and verify that each address is a valid address before they start sending unsolicited or spam messages. To reduce the possibility of receiving spam emails, there are things you can do to protect your email addresses and accounts, on your computer. The following tip will help you and your company combat the amount of spam you receive
Tips for End-users on Handling Spam Emails
Dos
- Check the privacy policy of websites or companies before you provide any personal information when filling out web registration forms, online surveys, etc.
- Look for options in websites or emails that allow you to unsubscribe from receiving further emails, offers or other marketing information.
- Be careful when subscribing to free email account services, especially when filling in the account profile. Check the terms and conditions of the email service.
- Use the anti-spam solutions offered by your ISP, or install email filters to reduce the amount of spam email you receive.
- Whenever feasible, use separate email addresses for different purposes. For example, use one email address for public newsgroups or chat rooms, and another for personal email messages.
- Avoid using an email address that contains simple dictionary words, or common names. Spammers can use brute-force techniques to guess valid email address at a specific domain using words from dictionaries, or combinations of common words.
- Install and enable anti-virus software, and keep it up to date using the latest virus signatures. Enable real-time detection to scan for computer viruses, malicious code for active processes, executables and document files that are being processed.
- Install and enable personal firewall software.
- Apply the latest security patches/hot-fixes from product vendors to your operating system and/or the applications installed in your computer.
- Be cautious when opening emails and email attachments, especially when receiving emails from strangers.
- Simply delete emails from unknown senders or dubious sources because if you reply or click on any link in the email message from an unknown source, you are confirming to the unknown sender that your email address is a valid one.
- Check the “sent” folder or outgoing mailbox of your email programme (or webmail account) to see if there are any outgoing messages that were not sent by you. If there are such messages, your computer may have been hacked and used by spammers to send emails from your account. You should disconnect from the Internet immediately and scan your computer with anti-virus or anti-spyware software (make sure the software’s signatures are up-to-date).
Don’ts
- Do not disclose your personal information too readily, including your email addresses.
- Do not publish your email address on public websites, contact directories, membership directories, or chat rooms.
- Do not be caught out by the spammers’ favourite tricks, such as the use of subject headings like “Remember me?” that try to trick you into thinking you should know the sender.
Tips for Companies/Organisations on Handling Spam Emails
Companies can implement a variety of methods to reduce the amount of incoming spam, such as protecting company email addresses, using filtering software and adopting well-defined security measures for employee workstations and email servers.
- Establish and enforce clear information security policies, and educate staff not to respond to spam emails. By responding to spam emails, employees are actually confirming their company email address as a valid address to spammers.
- Restrict the use of office email addresses for personal messages or participation in newsgroup or chat rooms by employees.
- Use a web-based contact form on the company website. Ensure that site visitors use the form to contact the company, instead of via a company email address that may be vulnerable to spam harvesting.
- If you need to publish a business email address on your site, consider writing it in a way that makes harvesting by spammers more difficult. For example, write the email address as “info[at]xyz.com.hk” instead of “info@xyz.com.hk”, and consider adding a statement stating that the company does not wish to receive unsolicited emails, such as “No spam, please”.
- Use anti-malware software and solutions at your email gateway and at individual employee workstations to filter spam and virus infected emails.
- Install email filter software at the server level if your company has its own email server. Filtering software can screen incoming messages before they are delivered to staff.
- If your company uses a web-based email service from an ISP, they may provide you with a number anti-spam settings. To reduce the risk of mistakenly blocking non-spam messages, also consider adding a holding folder to the filtering system, so that messages can be reviewed before deletion.
- Adopt good security measures such as server hardening to protect your email server and web server from being hacked and used by third parties to send spam emails.
What can you do if you receive a spam email?
- Ignore and delete spam: this is the simplest and most effective way to handle junk emails. Never reply to a spam message.
- Report the case to your Internet Service Provider (ISP) attaching the header of the spam email. Most ISPs have service terms that prohibit subscribers from using ISP services for spamming activities. Depending on the policy of your ISP, a spammer may be warned, have their service suspended or even terminated;
- Report any suspicious activity to your Internet Service Provider. If the spam emails contain suspected fraudulent or illegal information pretending to be sent from an identifiable organisation such as a bank, you may also complain to the related organisation.
- Consider discarding or shutting down your current email address and creating a new one if your email account becomes clogged with spam messages.
In cases of email scam, the fraudsters hacked into the victim’s email account, checked the victim’s business correspondence with business partners. They sent an email to the victim using the same or similar email account of his business partner and claimed that the payment bank account had been changed who further requested the victim to deposit the payment for goods into the fraudster’s designated bank account.
- If you receive any suspicious emails, you should confirm the identity of the purported business partners or the authenticity of the requests by means of telephone before remittance so as to prevent from being deceived.